The so-called “iPhone ZeroSpy” or DarkSword hack is a highly advanced cyberattack tool that targets Apple iPhones. It is not a simple virus or a malicious app, but a full exploit system that uses multiple security flaws in iOS to gain access to a device. Researchers have found that it relies on a chain of vulnerabilities, including zero-day flaws, which were unknown at the time they were first used in attacks.
What is the DarkSword iPhone hack?
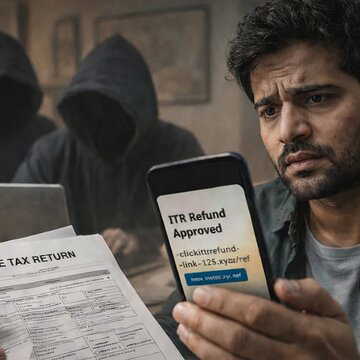
The attack can begin simply by visiting a compromised website. Without requiring any clicks or downloads, the exploit can silently enter the device and take control. Once inside, it can access highly sensitive information such as messages, call records, emails, photos, saved passwords and even cryptocurrency wallet data. Experts say the tool is designed to act quickly, stealing data within minutes and leaving minimal traces behind.
Also Read | Vivo X300 Ultra, X300s launch on March 30: Specs, design, camera details revealed
Who is at risk and how serious is it?
The threat mainly affects iPhones running older versions of iOS, particularly versions that have not received the latest security updates. Millions of devices could be vulnerable if they are not updated in time. The tool has reportedly been used by state-backed groups, surveillance firms and cybercriminals and has already appeared in multiple countries. What makes this threat more serious is its ability to take full control of a device without the user noticing anything unusual. It does not rely on suspicious downloads and can spread through seemingly normal websites. This marks a shift from targeted surveillance to potentially wider attacks affecting a larger number of users.
Also Read | 10 innovative tech devices from the 2010s that changed everyday life
However, experts say there is no immediate need to panic if your device is updated. Apple has already patched the vulnerabilities in newer versions of iOS. Keeping the phone updated, avoiding unknown links and using built-in security features can significantly reduce the risk.